|
Why Data Security Firewall?
The Firewall You Need Isn't the One You Have
"The world's most valuable resource is no longer oil, but data."
— The Economist, 2017 cover story
The future of cybersecurity depends on securing data itself — not just packets at the perimeter. The Data Security Firewall gives deeper visibility into the data threat surface, controls every transaction, and prevents exploitation of your organisation's most critical asset. Request a Demo Explore the Platform |
|
Yesterday's Firewall, Tomorrow's Liability
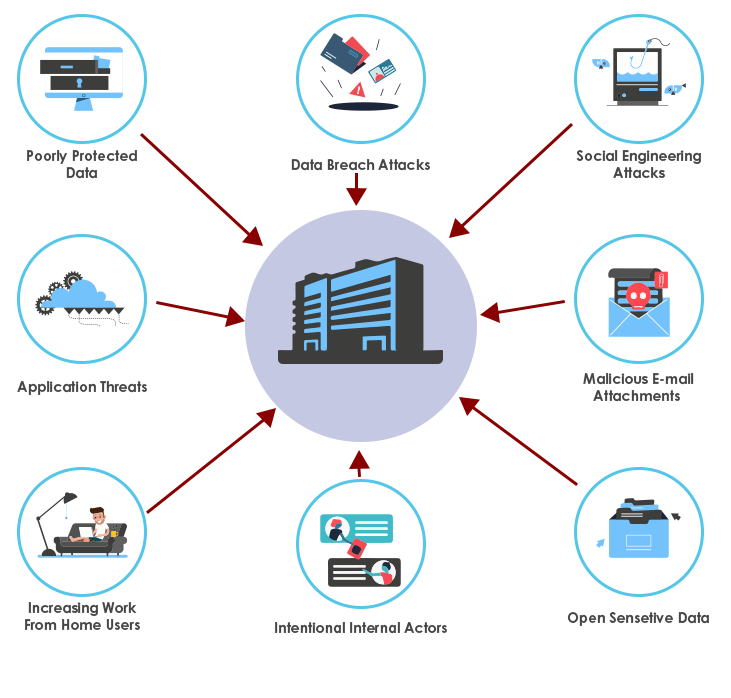
Cyber threats have shifted from purely external attacks to a mix of external attackers and internal actors — driven by hybrid work, cloud adoption, and SaaS proliferation. These sophisticated, blended threats need newer solutions that understand data flows, user behaviour, and contextual intent — not just protocols and ports.
Eight Reasons to Upgrade
How the GajShield Data Security Firewall differs from a traditional Next-Generation Firewall across the eight capabilities that matter most to a modern CISO.

01 · Threat Surface Monitoring & Control
|
DATA SECURITY FIREWALL
Two-Stage Categorisation, Real-Time HeatmapThe Data Security Firewall provides visibility into data threats that are critical for ensuring Data Security. A two-stage categorisation gives a deeper understanding of the threat surface, identifies policy violations, and generates an overall data security health indication. A built-in Threat Heatmap monitors violations and surfaces real-time threat patterns — enabling quick identification of anomalies and immediate action. |
NEXT-GENERATION FIREWALL
Perimeter-Level OnlyThe Next-Generation Firewall prevents general threats at the perimeter level only — it lacks visibility into the zero-day data threat surface. Without data visibility, it cannot provide deeper information on data threats or exploitation. Threat surface monitoring and control end up compromised or ineffective. |

02 · Deeper Data Visibility
|
DATA SECURITY FIREWALL
Beyond the Seven OSI LayersThe Data Security Firewall provides detailed, granular, and the deepest possible data-level visibility. It collects information on every transaction beyond just the traditional seven layers, including:
Letting you deep-dive into granular transaction details, generate reports, and set up data security policies at the right level of granularity. |
NEXT-GENERATION FIREWALL
Application-Level Only, No Data ContextThe Next-Generation Firewall has limited data visibility — essential for Data Security but missing here. With visibility restricted to application level only, it cannot analyse the data context of the application in use. This allows users to hide activities — data transactions on SaaS apps, web mail, social media, file sharing — resulting in undetected data leaks. |

03 · Approach Towards Security
|
DATA SECURITY FIREWALL
Data First ApproachThe Data Security Firewall uses a Data First Approach that scans and collects contextual data of every transaction, analyses the collected context against the organisation's Data Security Policies, looks for anomalies, and takes appropriate action to prevent critical data being sent out of the network. |
NEXT-GENERATION FIREWALL
Perimeter First, Data LastThe Next-Generation Firewall focuses on securing just the perimeter — analysing network protocols for security. By ignoring data as the core element of security, this approach fails to prevent data exploitation, which is what today's CISOs actually need. |
04 · Integrated Context-Based Data Leak Prevention
|
DATA SECURITY FIREWALL
Built-In Context-Sensitive DLPThe Data Security Firewall's integrated DLP solution prevents both intentional and unintentional data leaks across Web, SaaS, social media, file-sharing applications, and more — based on file content, file type, and file size. Its context-sensitive security also prevents data leaks via mail body, instant messengers, and other text communication platforms — based on multiple regular expressions and keywords defined by the organisation. Simple yet powerful, restricting data violations at the gateway. |
NEXT-GENERATION FIREWALL
No Built-In DLP, Bolt-On RequiredThe Next-Generation Firewall does not come with an integrated DLP solution. DLP is often a separate product entirely. Because of poor cross-platform integration, the bolt-on DLP lacks data understanding and context. The result: more false positives, more missed leaks, and less efficient DLP than a natively integrated solution. |
05 · Monitoring & Controlling SaaS
|
DATA SECURITY FIREWALL
Granular SaaS Transaction ControlThe Data Security Firewall monitors every SaaS transaction — uploads to Gmail, Google Drive, OneDrive, file-sharing services, social media — and applies policy decisions by file type, file size, and content. Control which SaaS apps users can access, what data they can upload, and what they can download — all from a single policy engine integrated with the firewall. |
NEXT-GENERATION FIREWALL
Blunt App-Level Allow/DenyThe Next-Generation Firewall can identify SaaS applications but cannot inspect what's happening inside them. Allow Gmail or block Gmail — that's the level of control. No way to say "allow Gmail but block uploading customer data spreadsheets" because the firewall can't see the data context. |

06 · Protection From Internal Threats
|
DATA SECURITY FIREWALL
UEBA-Backed Internal MonitoringInternal threats — whether from disgruntled employees, compromised credentials, or accidental policy violations — account for a large share of real-world data breaches but are commonly ignored by traditional firewalls. The Data Security Firewall uses User and Entity Behaviour Analytics (UEBA) to baseline normal behaviour for every user, then flags deviations — unusual login times, off-pattern data downloads, transfers to unsanctioned endpoints. Anomalies surface on the dashboard with full context for the security team to act on. |
NEXT-GENERATION FIREWALL
External Threats OnlyThe Next-Generation Firewall is designed to stop attacks crossing the perimeter from outside — it has no concept of internal users behaving suspiciously. With no behavioural baseline and no internal monitoring, the NGFW cannot distinguish between a regular user accessing files and a credential-stuffing attacker exfiltrating the same files. Internal threats slip through unnoticed. |

07 · Securing Roaming Users
|
DATA SECURITY FIREWALL
Enterprise Cloud Brings Roaming Users HomeRoaming users are the most accessible targets for attackers. They carry sensitive data on devices that, once disconnected from the corporate network, become entry points for cyberattacks. Using Enterprise Cloud, GajShield routes all roaming-user network traffic through the firewall at HO — bringing them back under the secured network. Every Data Security Policy applies to remote employees just as it does to those in the office, without impacting device performance. |
NEXT-GENERATION FIREWALL
Network-Bound, Off-Network BlindThe Next-Generation Firewall protects only employees within its secured network. Once a user steps outside the network perimeter, the firewall becomes ineffective. Roaming users get no visibility, no policy enforcement, no protection — leaving them as the most vulnerable entry point to the organisation's network for cyber attackers. |

08 · Data Health Criticality Indicator
|
DATA SECURITY FIREWALL
First-of-Its-Kind Data Health IndicatorThe Data Security Firewall features a Data Health Indicator that shows the overall health of data flowing through your organisation. Tag your data security policies by criticality, and the firewall keeps an eye on what's leaving the network. Based on the criticality assigned to each policy, it generates reports indicating the criticality of data being sent out via various platforms. First of its kind — not just blocking violations, but giving leadership an organisation-wide view of data movement to inform policy decisions. |
NEXT-GENERATION FIREWALL
Network Health, Not Data HealthThe Next-Generation Firewall reports on traditional perimeter security metrics — throughput, dropped packets, blocked connections. It doesn't hold data as a core element. With no data visibility, the NGFW cannot generate a report that emphasises data health. Instead it relies on network-level metrics for overall security health — an approach that's losing relevance as organisations move to hybrid network infrastructures. |
These are just a few of the key functionalities that differentiate the Data Security Firewall from a traditional Next-Generation Firewall — and why over 15,000 organisations across five continents have chosen GajShield to protect what matters most.
Want a Live Demo of the Data Security Firewall?
Talk to a GajShield security expert. We'll review your current firewall deployment and demonstrate exactly what your Next-Generation Firewall is missing.
Request a Free Demo Explore the Platform Download Brochure ↓